Scaled Access ROI
Return on investment
Whether you want to replace a homegrown solution or an existing vendor, the investment you make in us will be a good one.

Faster, autonomous automation
- Saving back-office resources with self-service access
- Reduce costs of maintaining homegrown solutions
- IT Architecture conceived for faster time to market
- Increased customer, business, developer productivity
- Reducing the cost of managing access change

New revenue
- Fast organic growth through access sharing
- Data-driven insights to increase conversion & engagement (zero-party, first-party & relationships data)
- Build new services & enhance customer experience triggered by access-related events

Less administration
- Improving audit performance
- Lowering the cost of compliance
- Lowering risk and cost with proven solution
- Integration with widely used Identity Providers
- Comes with GDPR compliance, including user-to-user consent
| Increased | Decreased |
|---|---|
| 1.2 to 10 x user base growth | Freeloaders sharing passwords |
| Developer satisfaction | Management hours |
| Ecosystem scalability | Risk & costs |
| Data-driven insights to increase conversion & engagement | Time to market |
| Group accounts | Help-desk costs |
| Win-back programs | Compliance & audit budget |
| Trial offerings |
Game-changer in access management
| Sharing Access | Self-service Access | Personalised Access | |
|---|---|---|---|
| Convenience | Let your users securely share the access you’ve given them | Access on the spot | Relevant & recommended |
| Security | Relationship-based access control; no password sharing | Validation workflows | Least privilege; Consent 2.0 |
| Impact | Drive fast organic growth | Operational efficiency | Superior user experience |
Our externalized authorization enables distributed organizations like yours to open up & scale their services to different people and parties within any specific ecosystem.
Get in touch.Other Whitepapers

The Developer’s Guide to Relationship-based Access Control
Start implementing Relationship-based access control. Your databases likely contain a network of entities and their relationships already.
Whitepapers
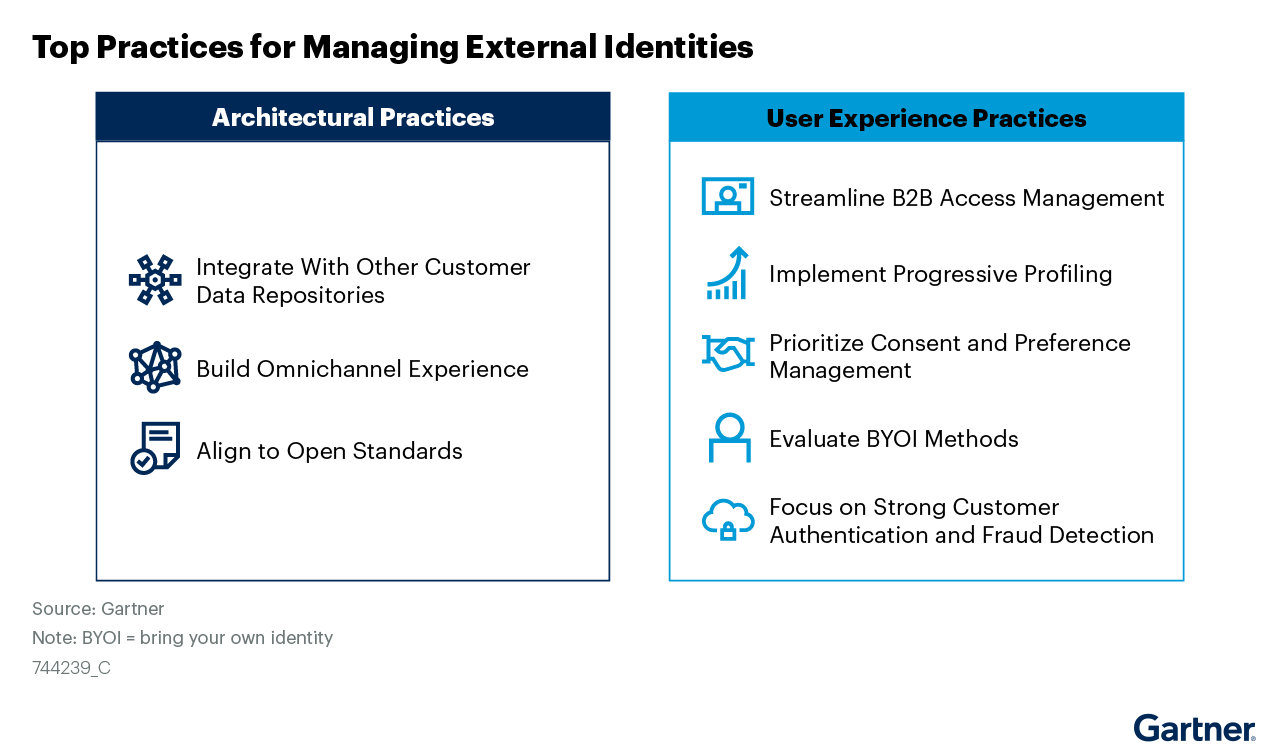
Managing External Identities Using a Customer Identity and Access Management Tool
Use this Gartner® research to learn how to implement a cohesive customer access management solution that lets customers, partners, and gig workers access your applications.
Whitepapers

Nine Common Access Management Misconceptions Debunked
It’s about time to clear up some common misconceptions about access management. Here’s a list of the traditional views that no longer hold true.
Whitepapers

Consumers Value Sharing. Security Will No Longer Stand in Their Way.
Authorization management has evolved to meet consumer sharing expectations and habits that they have acquired through social media, while ensuring security and privacy.
Whitepapers

How authorization technology will revolutionize the way we collaborate
Advanced access control systems let stakeholders, both inside and outside the organization, conveniently share information, knowledge and functionalities.
Whitepapers

Monetize a Loyal Audience without Alienating more Casual Viewers who want to Sample Content
How publishers & broadcasters use advanced CIAM technology to grow and engage audiences and convert casual viewers.
Whitepapers

Accelerating Secure OAuth 2.0 Compliant Advanced Authorization: Authlete & Scaled Access
Read how Authlete and Scaled Access’s combined solution enables organizations to build and operate OAuth 2.0 compliant authorization servers
Whitepapers

Data Protection:
From Obligation to Opportunity
GDPR leverages significant opportunities in terms of engagement and customer retention.
Whitepapers

10 Reasons to Buy an Access Management Tool Rather Than Build
Think cost is the important factor? Think again.
Whitepapers

Sharing Confidential Data Doesn’t Require Sharing Credentials
Read how advanced authorization platforms provide an alternative to credential sharing.

