Monetize a Loyal Audience without Alienating more Casual Viewers who want to Sample Content
Know your Audience, in order to Engage them Properly
First things first, you must know your audience in order to effectively engage them.
The UX is meant to accurately predict what viewers want at what stage and make signing up and accessing content as easy as possible.
It starts with understanding your audience’s full customer journey from beginning to end and includes all customer touchpoints and pain points. From occasional viewers who become regular viewers who eventually become subscribers.
Registration, Cookies, and Improved Customer Experience
Registration is typically one of the very first flows that are triggered. Registration is when an unknown person becomes a known person.
Registration provides zero-party data (data explicitly provided by the user) which is very valuable for subscription and advertising purposes.
Getting users to register is becoming more important for publishers in a world without third-party cookies. Until now, publishers have used third-party cookies to anonymously track individuals across the Internet to help them pair the right ad with the right users.
Growing data privacy demands and tighter regulations mean that publishers can no longer rely on cookies. Apple and Firefox have already blocked third-party cookie tracking by default on their browsers, while Google will eliminate third-party cookies completely from its Chrome browser by 2022.
Both zero-party data and first-party data (behavioral information generated by users) are now key for improving the customer experience.
Publishers need to drive user action and incite users to sign up. They will need to offer a customer experience (CX) that is superior to that of their competitors.
Both zero-party data and first-party data are now key for improving the user experience.
Publishers need to drive user action and incite users to sign up.
To achieve this, registration needs to be as frictionless as possible. It’s vital to present users with a clean, intuitive signup process that’s comfortable, satisfying, and engaging whether they’re signing up for a free trial, paid subscription, or just a newsletter.
86% of users say overly long forms make them quit during registration. A study found that reducing the number of form fields from 11 to 4 increases conversion rates by 120%. Publishers should therefore progressively profile their customers at key digital touchpoints and slowly build up the customer’s profile over time.
Paywall Management
Publishers typically use a paywall as a revenue strategy. A paywall is when some of the content is placed behind a “wall”. To bypass the paywall, users are prompted to register for a subscription. A subscription gives users access to digital content beyond the paywall and to multiple functionalities such as manage & pay subscriptions. Once registered, users are issued an access token that contains what they are allowed to view or do. The scope of access depends on the type of paywall the publisher chooses to install. Publishers need to deploy an access management solution that’s in sync with their paywall strategy.
Types of paywall:
- Hard paywall: only users with a paid subscription can access any of the content on the entire site. (WSJ)
- Freemium paywall: users can browse a portion of the website at no cost but have to pay for content that the publisher tags as quality content (used by nearly 45% of publishers).
- Sampling/Metered paywall: registered users can access a fixed number of content pages for free but have to pay to access more.
- Trialing: users receive a 24h guest pass in exchange for zero-party data such as an email addresses or are offered a month’s trial for just €1.
Access through Tokens not Cookies
Publishers should use access tokens to give access to content, not cookies. Cookies are less secure as they have a long lifespan and are stored within the browser memory over a long period of time. Hackers can get access to cookies through malware and use them for an impersonation attack, meaning they present themselves as being the registered user. Tokens are much more difficult to intercept and even if they get hacked, their lifespan is shorter.
Additionally, Cookies are device-dependent, whereas tokens are device-independent. This guarantees that registered viewers only get access to the actual scope you have defined as opposed to having your pre-given scope multiplied by the number of devices they are using.
Cookies are also browser-based so they do not work on a mobile app. Plus, cookies are disabled in private browsing mode which accounts for 20% of internet users.
CMS – Decapitated!
Another reason why publishers are opting for token-based security is that it allows them to implement a ‘Headless CMS’ architecture. ‘Headless CMS’ is no longer a buzzword and an increasing number of publishers are adopting it.
A ‘Headless CMS’ architecture is necessary to support various touchpoints of the customer journey. In a headless approach, the UI, front-end, and custom integrations are separated from the enterprise application implementation. The enterprise application exposes functionality via built-in APIs.
Access Rules
Access management helps publishers convert viewers into subscribers by offering access permissions that are appealing to particular user segments. Publishers define their access rules within the back end/content repository.
Access management helps publishers convert viewers into subscribers by offering access permissions that are appealing to particular user segments.
The Scaled Access solution offers publishers the ability to control metering settings from their end of the line. Our authorization management platform lets publishers build rules using XACML concepts such as:
- User or subject attributes
- Resource or content attributes (what counts within a meter)
- Actions (view content, but also manage & pay a subscription or engage with the writer)
- Context (subscriptions with desktops have a higher conversion)

Trust is the Currency of Interactions
Maintaining compliance with data privacy regulations like GDPR and CCPA is critical. Doing so won’t just put you ahead with regulators. It will also demonstrate your respect for user privacy. People want to know both how their personal zero-party data will be used and who will be using it within the new context of economic and social sharing.
That’s why our platform enforces consent during authorization decisions. We make sure that the user has given consent to the access and use of their personal data before any authorization is given.
In an era of content sharing, not only do we offer user-to-organization consent but also user-to-user consent. Scaled Access consent follows the Kantara guidelines:
- Consent Record Creation
- Human-Readable Receipt
- Links to Privacy Notices and Policies
- What Information is Collected
- Purposes of that Collection
- Information on Disclosure and Usage
Share Content, Without Sharing Passwords
Subscribers share the content they love, even paywalled content. In order to bypass the paywall, 1 out of 5 subscribers will share their username and password with the person they sent the article or video to. Publishers want to restrict this type of sharing, even though this goes against the views of some of their journalists.
We see things differently. To us, sharing content is an opportunity to let subscribers drive organic growth. That’s why we built a solution that lets subscribers share content sharing without sharing their credentials.
Sharing content is an opportunity to let subscribers drive organic growth.
We give publishers the ability to allow their subscribers to invite friends, family, or colleagues to view content they like. And no… it doesn’t mean opening up Pandora’s box. The publisher gets to decide who subscribers can share their content with and the type of access invitees get once they’ve signed up.
Here are two examples of how publishers can turn content sharing into an opportunity:
- Publishers can empower subscribers to generate new users by letting them share a story with non-subscribers provided they enter an email address (deployed by Tech site ‘The Information)
- Publishers can use social media sharing as an invitation flow. For example, WSJ offers 24-hour guest passes for non-subscribers, an offer that pops up when readers access a story shared by a subscriber or a journal on social media. (If the reader doesn’t enter their email address, they just get to read the one story.)

Group Subscriptions
Publishers that want to offer group subscriptions like family or enterprise subscriptions should use an access management solution that provides delegated administration. Delegated access lets subscribers easily and securely invite their family or colleagues to get access without sharing their credentials.
Invitation flows will help publishers drive fast organic growth and help prevent freeloading at the same time as users will be encouraged to invite others instead of sharing their passwords.
Network Insights
Publishers should not limit themselves to zero-party and first-party data for personalization. They should use a solution like Scaled Access that provides network insights. Knowing who invited who, lets you leverage recommender systems to increase conversion and engagement. You can recommend relevant content, offers, and ads to invited users based on the viewing habits or profile of the subscriber who invited them. Scaled Access will allow you to cater to your target audience’s needs and preferences at a whole new level.
Other Whitepapers

The Developer’s Guide to Relationship-based Access Control
Start implementing Relationship-based access control. Your databases likely contain a network of entities and their relationships already.
Whitepapers
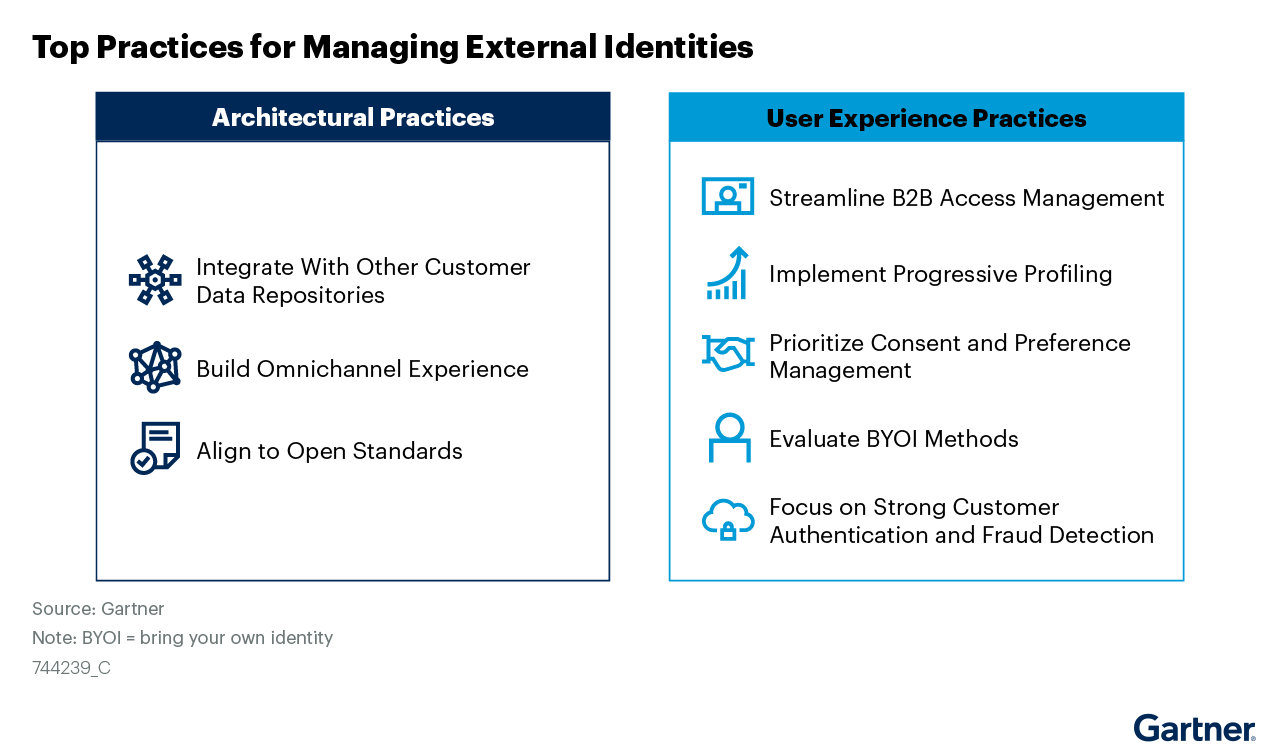
Managing External Identities Using a Customer Identity and Access Management Tool
Use this Gartner® research to learn how to implement a cohesive customer access management solution that lets customers, partners, and gig workers access your applications.
Whitepapers

Nine Common Access Management Misconceptions Debunked
It’s about time to clear up some common misconceptions about access management. Here’s a list of the traditional views that no longer hold true.
Whitepapers

Consumers Value Sharing. Security Will No Longer Stand in Their Way.
Authorization management has evolved to meet consumer sharing expectations and habits that they have acquired through social media, while ensuring security and privacy.
Whitepapers

How authorization technology will revolutionize the way we collaborate
Advanced access control systems let stakeholders, both inside and outside the organization, conveniently share information, knowledge and functionalities.
Whitepapers

Scaled Access ROI
Whether you want to replace a homegrown solution or an existing vendor, the investment you make in us will be a good one.
Whitepapers

Accelerating Secure OAuth 2.0 Compliant Advanced Authorization: Authlete & Scaled Access
Read how Authlete and Scaled Access’s combined solution enables organizations to build and operate OAuth 2.0 compliant authorization servers
Whitepapers

Data Protection:
From Obligation to Opportunity
GDPR leverages significant opportunities in terms of engagement and customer retention.
Whitepapers

10 Reasons to Buy an Access Management Tool Rather Than Build
Think cost is the important factor? Think again.
Whitepapers

Sharing Confidential Data Doesn’t Require Sharing Credentials
Read how advanced authorization platforms provide an alternative to credential sharing.

