The 5 Biggest Opportunities Access Management Offers the Consumer Internet of Things (IoT)
Access management has, up till now, played an unnoticed role in the consumer Internet of Things (IoT). It’s surprising because consumer IoT ecosystems are complex networks requiring flexible yet secure access management to ensure smooth running.
Here are the 5 biggest opportunities access management offers consumer IoT:
- Improve the multi-user experience
- Secure the device installation and hand over process
- Secure the IoT infrastructure – device to back-end and device to device
- Enforce consent and privacy choices in line with GDPR recommendations
- Provide better insights into the userbase and device use
1. Improve The Multi-User Experience
The multi-user experience is the driving force behind the growth of IoT. People share smart home devices with their families and guests. Improving this experience – both the security and usability – is key to unlocking greater value.
Not all households are equal. Here are some examples of how different relationships require different access:
| Relationship | Access level |
| Parent-Child | Limited usage of the smart device |
| Homeowner – Household Staff | Access limited to the weekdays they come to work |
Advanced access platforms provide predefined access rights for each relationship type, so you don’t have to do it all yourself.
Access limitations not only depend on relationships. There are other dimensions, such as:
| Access Limitation | Use Case |
| Privacy | giving guests anonymous access (e.g., to people renting your home) |
| Payment | letting a user pay to access your device (e.g., an electric car charger) |
| Functionality | letting a user regulate smart lighting but not smart heating |
2. Secure The Device Installation & Hand Over Process
Modern access platforms secure the device installation and hand-over process.
Let’s take smart locks as an example. Currently, installers set up the device and then hand over the device credentials to the owner. This type of installation has two issues:
- How can the homeowner ensure that only certified installers can install their device?
- How can the homeowner ensure that the installer will not be able to access the device after they handed over the credentials?
Advanced access platforms solve the first issue by ensuring that the installer has been authenticated and verified as a certified installer before they get to install. These platforms use validation workflows to match the installer’s certificates against an authoritative source.
The second issue is solved by allowing the installer to invite the homeowner to get access without sharing credentials. The owner gets a separate administrator account.
As soon as the owner is set up, the installer loses access and can’t operate the device without permission from the owner. If the same professional – or a different one – comes back for maintenance, they’ll only be able to access the device after being permitted by the owner.
Once the maintenance has been completed, the admin can easily disable access for the professional, ensuring absolute security.
3. Secure the IoT Infrastructure
Access platforms help secure the ever-growing IoT ecosystem and infrastructure. It’s a simple, obvious, but definite statement.
Securing the IoT ecosystem is no longer simply about securing the 3-way communication between a user, a device, and the IoT back-end system.
The IoT landscape contains intercommunication between different devices and different back-end systems, and this infrastructure is continuing to expand. Leading research giants like Gartner have predicted that by 2023 there will be 43 billion connected devices worldwide1.
Increased growth means increased risk. Put: as the IoT ecosystem continues to grow, so too does the risk of cyberattacks. Hackers have more entry points and routes to attack.
Info Security Magazine reports that a security vendor detected 100 million cyberattacks on IoT endpoints in the first half of 2019 alone2. It’s worrying, to say the least.
State-of-the-art access management helps secure the landscape and communication between different entities. It provides access tokens to both IoT devices and IoT back-ends.
Using access tokens throughout the ecosystem helps ensure only authentic devices and back-end systems access the infrastructure.
The benefits of access tokens go further, though. They remove the need for an application to require the user’s credentials for every access request. This massively reduces the risk of a user’s credentials being compromised and their device being targeted by a hacker to access the back-end and attack the infrastructure.
Access platforms help secure the ever growing
IoT ecosystem and infrastructure.
It’s a simple, obvious, but definite statement.
4. Enforce Consent & Privacy Choices in Line with GDPR Recommendations
When multiple people share a device, consent and privacy concerns need tackling:
- Sharing devices shouldn’t automatically mean others get to see your personal information without your knowledge. How to enforce users’ consent?
- Sharing devices shouldn’t automatically mean that others get to see how you use the device. How can users control this?
Access management tools give people this control. It ensures a user’s consent is always enforced before access is given (denied or withdrawn) to their data. For example, a babysitter wouldn’t be able to see the personal details of the homeowner.
These platforms can also push a user’s delete data request to any back-end system that stored personal information about them.
But, it goes further than that. They manage the lifecycle of a users’ consent and ensure that a repository of all the recorded consents a user has given or denied over time exists. Consent receipts can be retrieved should unlawful data access disputes occur.
Users choose whether others can track how they use the device. The access platform enforces these choices. For example, you don’t want your landlord to see how you use devices.
5. Provide Better Insights Into The Userbase & Device Use
Access platforms provide IoT vendors with better insights into how their devices are being used.
Consumer IoT devices, ingenious home appliances, are used by multiple users, yet vendors struggle to see who is actually using their device and how. By unlocking a more accurate userbase, this information can help IoT vendors in two areas: product management and marketing.
Advanced access platforms let device owners share their devices with friends and family without sharing credentials. One device may be linked to multiple individual accounts. IoT vendors get to see how many users use their devices and how they actually interact on an individual level. This unique knowledge helps vendors improve their product management, build better products and target their marketing.
Conclusion
Advanced access management within consumer IoT offers enormous benefits to device owners, users, and vendors. And, as the consumer IoT continues to develop, so will the opportunities and importance of access platforms.
Consumer IoT ecosystems are complex networks, requiring flexible yet secure access management
to ensure their smooth running.
1 Forecast: Internet of Things — Endpoints and Associated Services, Worldwide, 2017, Gartner, December 2017, gartner.com.
2 https://www.infosecurity-magazine.com/news/over-100-million-iot-attacks/
Other Whitepapers

The Developer’s Guide to Relationship-based Access Control
Start implementing Relationship-based access control. Your databases likely contain a network of entities and their relationships already.
Whitepapers
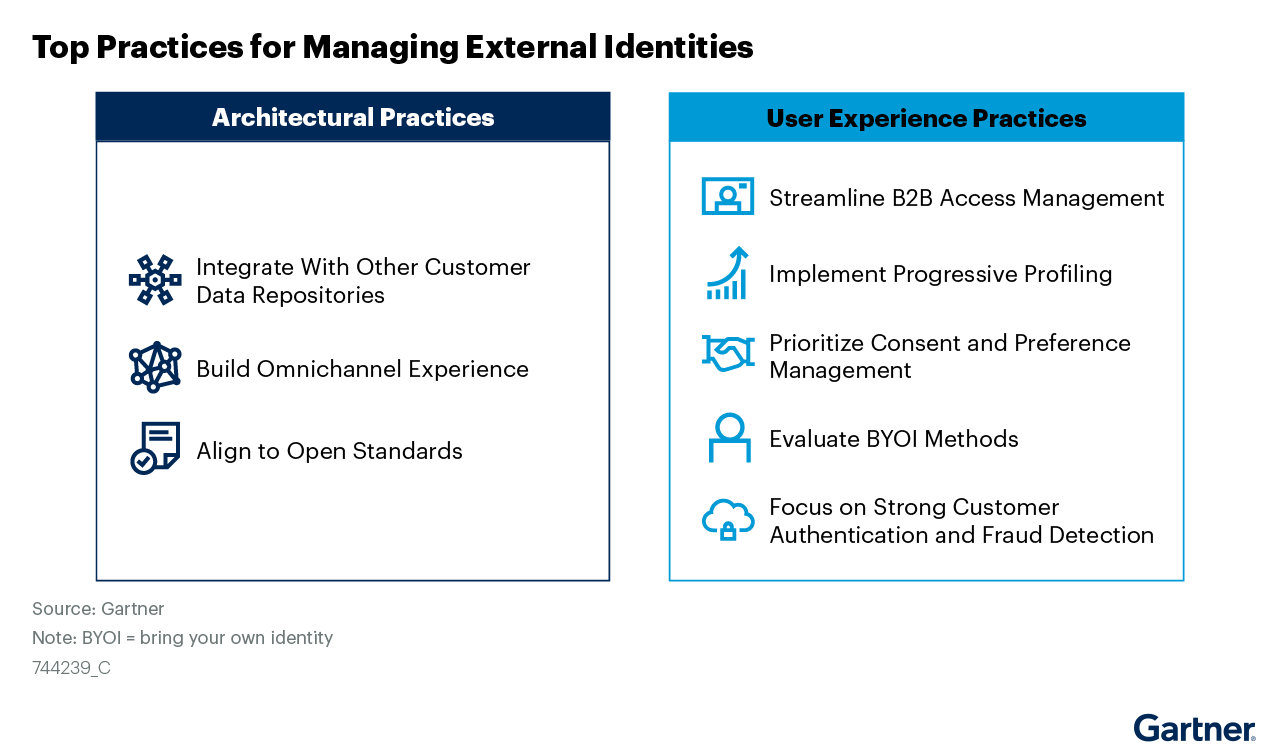
Managing External Identities Using a Customer Identity and Access Management Tool
Use this Gartner® research to learn how to implement a cohesive customer access management solution that lets customers, partners, and gig workers access your applications.
Whitepapers

Nine Common Access Management Misconceptions Debunked
It’s about time to clear up some common misconceptions about access management. Here’s a list of the traditional views that no longer hold true.
Whitepapers

Consumers Value Sharing. Security Will No Longer Stand in Their Way.
Authorization management has evolved to meet consumer sharing expectations and habits that they have acquired through social media, while ensuring security and privacy.
Whitepapers

How authorization technology will revolutionize the way we collaborate
Advanced access control systems let stakeholders, both inside and outside the organization, conveniently share information, knowledge and functionalities.
Whitepapers

Monetize a Loyal Audience without Alienating more Casual Viewers who want to Sample Content
How publishers & broadcasters use advanced CIAM technology to grow and engage audiences and convert casual viewers.
Whitepapers

Scaled Access ROI
Whether you want to replace a homegrown solution or an existing vendor, the investment you make in us will be a good one.
Whitepapers

Accelerating Secure OAuth 2.0 Compliant Advanced Authorization: Authlete & Scaled Access
Read how Authlete and Scaled Access’s combined solution enables organizations to build and operate OAuth 2.0 compliant authorization servers
Whitepapers

Data Protection:
From Obligation to Opportunity
GDPR leverages significant opportunities in terms of engagement and customer retention.
Whitepapers

10 Reasons to Buy an Access Management Tool Rather Than Build
Think cost is the important factor? Think again.

